SSH w/o a Password!
System Administrator II by Day, Front-End Developer by Night, PhD Student
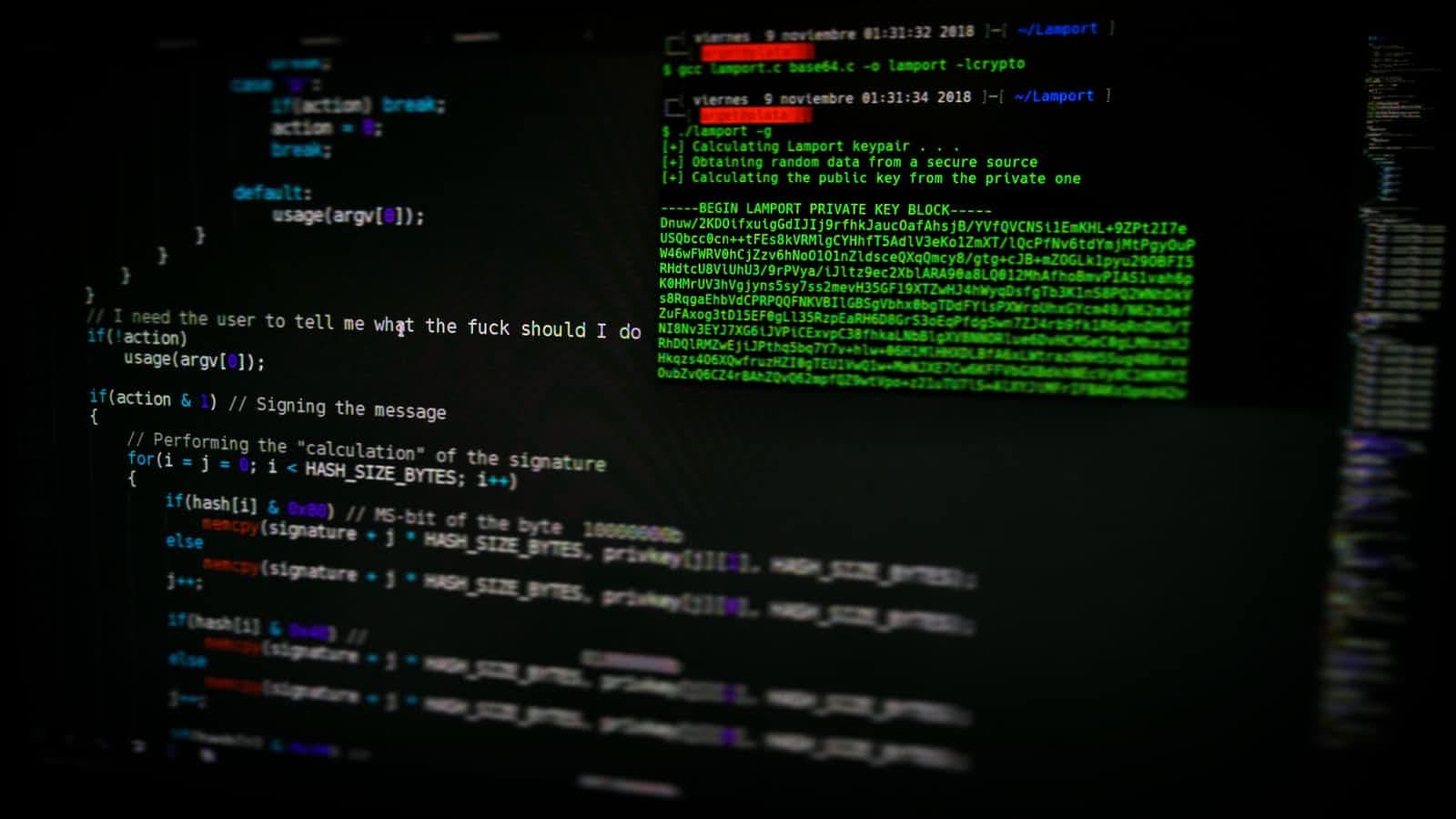
SSH, which also stands for Secure Shell, is something that I currently use to connect to my Linux machines to run maintenance on them. I have a couple of Linux-based machines that I routinely need to log in to either fix something or apply some kind of maintenance to them. SSH is the easiest way I can access them to run terminal commands that I need to routinely run.
With this being said, something that takes time is having to retype the password over and over again to access the machine in the local network from the same machine. Because of my drive to always try to accomplish repetitive tasks more efficiently, I was led to find a way to access the drives more efficiently. Because of that, I ended up implementing this process of using Private/Public Keys as authentication into the systems. With these steps being implemented, I do not need to type my password in when I SSH into the same systems again.
Please note that this only works for the specific client you are SSH from and the machine you are SSH into. You will need to repeat that process for every other situation that you are connecting to.
Some disclaimers for this process:
Disclaimer This is only for a one to one connection. If accessing same system via another machine, you will need to repeat the steps or type a password in to access system.
Second Disclaimer Do this at your own security risk.
Windows Based Instructions
Create your .ssh directory!
mkdir C:\Users\<username>\.ssh
Create a Public and Private Key!
ssh-keygen -f C:\Users\<username>\.ssh\id_rsa -t rsa -P ""
Copy the Public Key over to the system that you are accessing!
type C:\Users\<userdirectory>\.ssh\id_rsa.pub | ssh <username>@<server-ip-address> -o StrictHostKeyChecking=No "umask 077; test -d .ssh || mkdir .ssh ; cat >> .ssh/authorized_keys || exit 1;"
Now Test!
Mac Based Instructions
You don't have to make a directory here on macOS/Linux based machines. It already exists!
Creating a Public and Private Key!
ssh-keygen -f ~/.ssh/id_rsa -t rsa -P ""
Copy the Public Key over to the system that you are accessing. There are two ways that you can do it.
You can do this ssh-copy-id (this way will require a password):
ssh-copy-id -i ~/.ssh/id_rsa.pub <username>@<server-ip-address> -o StrictHostKeyChecking=No
Or you can use cat:
cat ~/.ssh/id_rsa.pub | ssh <username>@<server-ip-address> 'mkdir -p .ssh; cat >> .ssh/authorized_keys'
Now Test!
After this process, you should be good to go and connecting to your machines via SSH without a password.
I hope this helps! I did post these instructions earlier in the week on my Twitter account! Feel free to follow me on socials here! - links.seanmilfort.com